08.25
This article will show you how to handle tape backups generated by NTBackup, turn them into a .BKF file (using Linux) and extract specific files (using Linux/Windows). Some of the stuff explained here may also be useful when dealing with corrupt tapes/files, and may work for any backup software that generates MTF (Microsoft Tape Format) output, such as maybe Symantec Backup Exec1.
The scenario: an old machine (hosting a not so important app) crashes badly due to multiple disk failures. O.S. (Windows 2000 Server) won’t boot anymore. Backups were directed to a local DDS tape drive, the only one of its kind surviving in the whole Company. While reinstalling the app to another server, I need to recover some files and have access to the pre-crash registry.
And here’s the plan:
- Boot the half-dead server with the invaluable SystemRescueCd.
- Put the last available tape backup in the drive.
- Save an image of the tape somewhere.
- Extract stuff from the image.
When SystemRescueCd is running and network connected, make available a shared folder:
root@sysresccd /root % mount -t cifs //fileserver/e$ /mnt/storagespace -o username=administrator,workgroup=domain.local
Then, generate the image. NTBackup tape backups are spread across multiple “tape files”. If you read the tape from the beginning, sooner or later you will hit EOF (an end-of-file condition). Don’t rewind it: go on to the next file instead. Repeat until there are no more files to read.
On Unix, the first SCSI tape device is mapped to /dev/st0 and /dev/nst0. When a process finishes reading from /dev/st0, the tape is implicitly rewound. Viceversa, using /dev/nst0 doesn’t cause any rewind; tape will stay positioned right after the last block read.
Just in case, perform a manual rewind:
Then, try to guess the right block size. It seems to be set at 16K. Should this method fail, check the “How do I find out tape block size?” method here.
SCSI 2 tape drive:
File number=0, block number=0, partition=0.
Tape block size 16384 bytes. Density code 0x26 (DDS-4 or QIC-4GB).
Soft error count since last status=0
General status bits on (41010000):
BOT ONLINE IM_REP_EN
Start reading (by means of dd) with the specified block size. See? We’re using the non-rewinding tape device /dev/nst0.
06g" $f`.bin ibs=16384; done
dd if=/dev/nst0 of=tapeblock000001.bin ibs=16384
dd if=/dev/nst0 of=tapeblock000002.bin ibs=16384
dd if=/dev/nst0 of=tapeblock000003.bin ibs=16384
dd if=/dev/nst0 of=tapeblock000004.bin ibs=16384
dd if=/dev/nst0 of=tapeblock000005.bin ibs=16384
dd if=/dev/nst0 of=tapeblock000006.bin ibs=16384
dd if=/dev/nst0 of=tapeblock000007.bin ibs=16384
dd if=/dev/nst0 of=tapeblock000008.bin ibs=16384
dd if=/dev/nst0 of=tapeblock000009.bin ibs=16384
dd if=/dev/nst0 of=tapeblock000010.bin ibs=16384
root@sysresccd /mnt/storagespace/temp % dd if=/dev/nst0 of=tapeblock000001.bin ibs=16384
1+0 records in
32+0 records out
16384 bytes (16 kB) copied, 0.0341089 s, 480 kB/s
root@sysresccd /mnt/storagespace/temp % dd if=/dev/nst0 of=tapeblock000002.bin ibs=16384
270540+0 records in
8657280+0 records out
4432527360 bytes (4.4 GB) copied, 7666.22 s, 578 kB/s
[..]
root@sysresccd /mnt/storagespace/temp % dd if=/dev/nst0 of=tapeblock000007.bin ibs=16384
4+0 records in
128+0 records out
65536 bytes (66 kB) copied, 0.1176 s, 557 kB/s
root@sysresccd /mnt/storagespace/temp % dd if=/dev/nst0 of=tapeblock000008.bin ibs=16384
0+0 records in
0+0 records out
0 bytes (0 B) copied, 0.00461986 s, 0.0 kB/s
root@sysresccd /mnt/storagespace/temp % dd if=/dev/nst0 of=tapeblock000009.bin ibs=16384
dd: reading `/dev/nst0': Input/output error
0+0 records in
0+0 records out
0 bytes (0 B) copied, 0.00356835 s, 0.0 kB/s
Reads beyond the last file will result in an “Input/output error”.
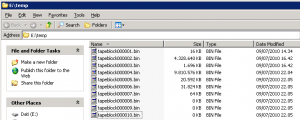
It’s time to join the .bin files into a single one: the tape image (maybe using HJSplit for the task). You could’ve been more clever than me and appended dd‘s output to a single file, thus skipping the join step and saving space. I didn’t do it because I wanted to see if any tape file was corrupted (and be able to re-read it, if needed).
I called the tape image “backup.bkf”, even though it’s not a true .BKF file… As we said, it’s a tape image. NTBackup is not able to read it, whereas the abundance of “BKF recovery” software can. Before going on, let me polemicize a bit. There are many, almost identical, software of this kind. I’ve got the feeling that they all “borrow” from this open source BKF reader2. Looks like different commercial developers grabbed the same source, embellished the GUI just a bit, and made a product to sell. How lame. But it turns out that you don’t need to pay a cent to extract files from a .BKF or tape image, on Linux or Windows as well.
On windows, get ntbkup by William T. Kranz . I use the (optional) -s3 switch to target set 3 which I know holds the System State.
NTBKUP Ver 1.07c compiled for WIN32 with MAX_PATH = 100
compiled for 64 bit file offsets
Copyright (C) 2003 William T. Kranz
NTBKUP comes with ABSOLUTELY NO WARRANTY
Free software distributed under the terms of the GNU General Public license
See http://www.gnu.org/licenses/gpl.html for license information
Check http://www.fpns.net/willy/msbackup.htm for Updates & Documentation
resrict operations to backup set 3
device name: C:
volume name: Local disk
device name: D:
volume name: Volume
Set 3:
Name: Company lun-29-06-2009-23.04
Description:
User: DOMAIN\administrator
device name: System state data from 0x36113d956 to 0x3611ec956
length 716800 atrib 0x20 05/14/2008 03:10:38 PM
extracing: default:
data from 0x3611ecd4e to 0x3611f2d4e
length 24576 atrib 0x20 06/29/2009 09:42:50 PM
extracing: SAM:
data from 0x3611f3156 to 0x3611fe156
length 45056 atrib 0x20 06/29/2009 11:00:07 PM
extracing: SECURITY:
data from 0x3611fe556 to 0x3621cb556
length 16568320 atrib 0x20 06/30/2009 01:35:59 AM
extracing: software:
data from 0x3621cb952 to 0x362487952
length 2867200 atrib 0x20 06/29/2009 10:42:23 PM
extracing: system:
data from 0x362487d2e to 0x3624aad2e
length 143360 atrib 0x20 06/04/2003 01:24:14 PM
extracing: userdiff:
Bingo, I can load the software hive with “reg load” (see here) and extract the keys I need.
Should you prefer so, download mtftar on your Linux box, compile it and run something like:
Extract the other files you need and voilà…